Network Security
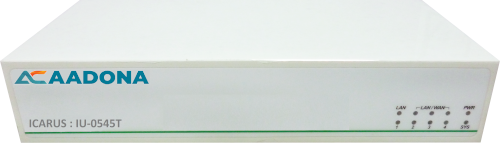
ICARUS : IU-0545T
-
Overview
NGUTM Network Security Enterprise -
4 Port Gigabit SMB UTM Firewall for up to 50 Concurrent Users
Best-suited UTM for SMB
IU-0545T is an ideal UTM designed especially for SOHO and SMB, a 9-inch desktop fanless design that ensures silent operation in small or quiet office environments.
Firewall
Built-in SPI (Stateful Packet Inspection) provides DoS detection and prevention against certain popular flood attacks like SYN, ICMP, and UDP. When unusually high rates of the new connection are detected, the system will issue an alert notification or block an anomalous session. In addition, IU-0545T SPI protects against packet-injection attacks by checking several components of TCP and UDP sessions.
Highest NAT Packet Processing Performance
Internet service providers (ISPs) are offering higher-speed DSL to homes and businesses. In order to satisfy existing customers, IU-0545T provides better support for the explosive growth in data traffic. In addition to Gigabit LAN and WAN ports, hardware-accelerated NAT operates at gigabit speeds up to 1.8 Gbps which makes IU-0545T a basic unit with comparable performance and advanced functionality.
IPv4 / v6 Dual Mode
Native dual-stack supported. To cope with IPv4 depletion, AADONA provides a solution that covers both IPv4 and IPv6 networks and can be configured for IPv4 only, IPv6 only, or to support both protocols simultaneously.
Content Filtering
IT administrators can configure Web filtering profiles that block URLs to inappropriate web pages like violence and pornography and hacking attacks like malware and virus. Moreover, IU-0545T filters out ActiveX objects, Cookies or Java applets that may pose a security threat in certain situations. Both keywords and URLs of specified websites can be added to Blacklist and Whitelist.
Anti-Virus
Clam AV for virus scanning can detect over a million kinds of viruses, worms, and Trojans. Once suspicious emails are detected, the administrator can decide to delete it automatically, quarantine ones with unwanted file extensions or send notifications. Moreover, websites will be scanned once the function of anti-virus is enabled in policy.
Inbound/Outbound Load Balance
IU-0545T supports outbound and inbound load balancing, providing businesses at least 2 WAN links. Multi-homing load balancing is supported to spread a business’s Internet traffic among multiple access links to increase the aggregate throughput and to divert traffic away from non-functional links when they fail. An additional 3G/4G/LTE USB can also be attached to the USB port of the IU-0545T to add backup wireless connectivity.
SDN WAN
IU-0545T combines MPLS, Ethernet ADSL, Wireless 3G, 4G/LTE in a single box. It is ideal for companies with multiple offices having demanding applications. IT Administrators can manage Internet access easily for improved latency and reduced WAN cost spending. Companies can adopt a reliable and private line MPLS to protect important data, while administrators cost-effectively mix and match other network links as backup links. With SD-WAN, geographic boundaries are erased. Network links can be optimized to support applications with specific needs.
QoS
QoS offers more agile bandwidth management for industries and organizations. All the servers and users can be configured for their minimum and maximum bandwidth; the remaining bandwidth will be allotted to the other users according to their configuration.
URL Database (One-Year License)
IU-0545T integrates a third-party URL database that collects millions of URLs and updates at regular intervals of time. All these URLs and their contents are analyzed and classified into categories. IT administrator is able to block any category in the database with ease without entering keywords or the desired URL addresses one by one. Users do not have to fear they might stumble on a malicious URL and get infected with malware.
Application Control (One-Year License)
In order to prevent data leakage and ensure regulatory compliance, access to applications which unrelated to work should be controlled during working hours. Cooperated with a third-party database, IU-0545T can enforce policies for applications like P2P, VPN and Remote Control, Streaming and VoIP, Network Service, Online Sharing and Storage, Web Service, Social Networks, Instant Messaging, System and Update, News and Media, Shopping and Auction, Entertainment and Arts, Sports and Travel, Food and Drink, Finance and Insurance, Gambling and porn, Games, etc. The URL database is updated daily at the time specified.
Intrusion Prevention System (IPS)
Built-in IPS inspects the packets from OSI layers 4-7 (transport to application layer) and blocks concealed malicious code and worms delivered in TCP/IP protocols. As soon as an attack is suspected, IT administrator will be notified immediately and later an extensive range of reports will be available for analysis. AADONA regularly updates the predefined attack signature database and makes it available as IPS security package.
Bulletin Board
A Bulletin board is an effective way designed to make an announcement to company employees. Before being allowed to use the Internet, employees are expected to read the messages posted on the bulletin board.
Authentication
IU-0545T offers three authentication methods: Active Directive (AD), POP3, and Radius. When a user first opens a web browser and begins to access an internet site, they will be prompted to authenticate before using the internet service.
Complete VPN Solutions
Using IPsec, PPTP, L2TP, and SSL VPN connections, IU-0545T provides data confidentiality, data integrity, and data authentication. At the same time, popular protocols such as web, SMTP, and POP3 that contains packets transmitting within tunnels can to be controlled.
Supports IPSec, PPTP, L2TP, SSL, and GRE Tunnel
Supports DES, 3DES, AES, AES128, AES192, and AES256 encryption and SHA-1, SHA256, SHA512, and MD5 authentication algorithms
SSL VPN mobility client for Android and Apple iOS
Controls connectivity of remote sites from the central location
Graphic Dashboard
The dynamic dashboard in the web user interface (web UI) presents a graphic view of the system status including concurrent connections, application classification, network resource usage, HTTP or HTTPS traffic, and intrusion defense to help in tracking and diagnosis. IT administrators are given visibility into the network users, their devices, and their applications.
Diagnostic Tools
IU-0545T provides diagnostic tools such as Ping, Traceroute, DNS Query, Port Scan, and so on. They make fault isolation and troubleshooting easy for administrators.
Flexible Policy Control
Flexible web policies allow you to build rules based on users, groups, dates, times, and much more. Administrators can setup combinations to reach different network requirements. Problems can be fixed without temporarily suspending services and operations can be made through GUI to keep your network safe and secure.
User-Friendly Interface
Firmware is upgraded using a web browser. Users can select their preferred time zone. IU-0545T export/import functionality makes it possible to exchange various configuration entities between one AADONA UTM and another.
Cloud-Based Service System (I-Cloud)
I-Cloud is a next-gen cloud service platform providing a user-friendly interface to support instant equipment maintenance and management. It is an all-inclusive solution to monitor various networking appliances deployed in either external or internal networks such as UTMs, wireless APs, or switches. When an anomaly occurs, administrators will be notified of the problem.
High availability
Building a cluster and hot standby of two or more AADONA UTMs is available.
Features
| Features | Description |
| Threats Defense (Anti-Virus/IPS/SSL Inspection) | Uses open source Clam AV engine with huge database includes millions of signatures Clam AV team has fast response time, updates signature regularly and requires no yearly subscription fees Provides IPS attack-signature database IPS risk management is divided into 3 levels (high, medium, and low) Provides scalable SSL inspection |
| Malicious URL Filtering (URL) | URL filtering policies are allowed to be configured by administrators |
| Firewall Security | Coordinated DoS/DDOS attacks and UDP Flood performed by hackers can be blocked automatically. Supports IPv4, IPv6, and Dual Stack Supports load balancing and fail-over for both outbound and inbound traffics Provides DNS Proxy and Dynamic DNS services |
| Potential Risks Detection (Flow Analysis) | Flow/behavior-based anomaly detection allows both up and down sessions to be analyzed and see if a performance problem exists An anomaly can be blocked, recorded, and notify subscribers. Switching topology |
| Application Access Control | Multiple application categories e.g. P2P, VPN and Remote Control, Streaming and VoIP, Network Service, Online Sharing and Storage, Web Service, Social Network, Instant Messaging, System and Update, News and Media, Shopping and Auction, Entertainment and Arts, Sports and Travel, Food and Drink, Finance and Insurance, Gambling and Porn, Games, etc. Free scheduled updates 3. Administrators can use policies to prohibit their users from accessing to applications |
| User Identity (Radius) | The host computers are established to ensure user identity and also supports the use of LDAP, Radius, AD or POP3 servers for authentication. Desired user groups can be customized Provides authentication record and connection status |
| Load Balance | Ensuring the network is never disconnected Provides inbound and outbound load balancing Load Balancing fail-over with 3G/4G USB Users can assign load balancing automatically, manually, or by source-destination IP |
| QoS | Supports bandwidth guarantee, max/min-limit, and priority commands Bandwidth usage from the internal/external source IP can be limited Efficient priority scheme is available |
| VPN Connection | IPSec, Site-to-Site PPTP, and L2TP VPN Reliable SSL VPN connection Users can create, edit, and control VPN connections Supports IP Tunnels |
| Operation Modes | Transparent Bridge, NAT |
| Logging & Reports | Multiple event logs can be centrally logged and monitored. And logging includes configuration, networking, and route, objects, services, advanced protection, mail security, VPN, etc. Dashboard (Optional) A report includes a statistic table, ranking grid, bar/line graphs, and pie charts. (included in the Dashboard module) |
| Virtual Server | IP Supports virtual server that data flows can be transmitted to any of the other ports without using any switch or router |
| High Availability | Building a cluster and hot standby of two or more AADONA devices is available |
| Cloud Management | Cloud-based integration can be led to AADONA I-Cloud service system Manages multiple UTMs Provides real-time monitoring and proactive management |
| Bulletin Board | An announcement can be made to employees in a very effective and proper way |
| Diagnostic Tools | Standard net tools such as Ping, Traceroute, DNS lookup, and port scanner are available to help users identify and fix connection problems. Test widgets like IP Route, Wake Up, SNMP, IPv6 tools are provided to test your connection and readiness as well. |
| Others | Free firmware upgrades Administrators can select authorized users and assign access conditions Supports 802.1Q Autonomous management based on a user-friendly interface Fanless design that ensures noiseless operation Quick setup wizard |
Specifications
| Model | IU-0545T |
| Recommended User Numbers | Up to 50 |
| Mounting | Desktop |
| Power supply | AC: 100V-240V |
| I/O Interface | |
| 10x100x1000 | 4 |
| USB | 2 |
| HDMI | 1 |
| Capacity | |
| Firewall throughput | 1.8Gbps |
| Max. Connections | 200000 |
| Antivirus throughput | 350 Mbps |
| VPN throughput | 200 Mbps |
| Software | |
| Firewall | Yes |
| Anti-Virus | Clam AV |
| Authentication | Yes |
| Anomaly IP Analysis | Yes |
| Typology | Yes |
| Load Balance | Inbound / Outbound |
| QoS | Yes |
| Intranet Protection | Yes |
| Applications Control | Lionic (1-year license) |
| URL Management & Database | Lionic (1-year license) |
| IPS & Signature Database | Yes |
| Dashboard | (Optional module, reports included) |
| HA | Yes |
| Bulletin Board | Yes |
| VPN (IPsec/PPTP/L2TP) | Yes |
| SSL VPN | Yes |
| IP Tunnel | Yes |
| I-Cloud Management | Yes |
| Warranty | 2 Year Default + 3 Year Warranty Pack, Total 5 Years |
| *All specifications are subject to change without notice. | |